What is risk management?
Definition
Risk analysis and risk management is a process that allows individual risk events and overall risk to be understood and managed proactively, optimising success by minimising threats and maximising opportunities and outcomes.
Definition from APM Body of Knowledge 7th edition

Risk management
Risk management is focused on anticipating what might not go to plan and putting in place actions to reduce uncertainty to a tolerable level.
Risk can be perceived either positively (upside opportunities) or negatively (downside threats). A risk is the potential of a situation or event to impact on the achievement of specific objectives
Working with the risk owner, the project professional ensures that risks are clearly identified before moving on to the risk analysis step of the risk management process.
The project risk management process reflects the dynamic nature of projectwork, capturing and managing emerging risks and reflecting new knowledge in existing risk analyses.
A risk register is used to document risks, analysis and responses, and to assign clear ownership of actions.
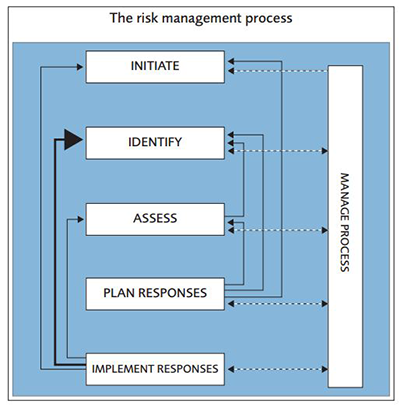
The risk management process
Source: Project Risk Analysis and Management Guide 2nd edition
Watch: What is risk?
What is risk analysis?
Risk analysis provides guidance on where the greatest vulnerabilities lie. Because risk analysis is fundamentally perception based, it is important for the project professional to engage stakeholders early to identify risks.
To make sense of differing perceptions, it is important to describe risk events clearly, separating causes (facts now), from risk events (situations that may occur), from effects (that have an impact on one or more of the project measures). This enables subsequent analysis and management of risks.
Effective risk analysis and contingency planning will see planned time and/or contingency used. Unused contingency is most likely caused by overestimation, luck or the efficient management of risk. Insufficient contingency is most likely caused by optimistic estimation, bad luck or inefficient management of risk.
Outputs from risk analysis help the project professional to:
- Understand the probability of achieving outturn dates, costs or
- Inform and influence decision-making about the chances of achieving the business case and
- Agree the level of contingency to provide the required level of confidence.
 APM Learning
APM Learning
The following risk management resources are available on APM Learning. This is a member only resource.
- Information sheet - Risk management
- Mini guide - Project risk analysis and management
 The Asymmetry between Threats and Opportunities in Risk Management
The Asymmetry between Threats and Opportunities in Risk Management
Results from a Survey among APM Corporate Members
Our latest survey was conducted among our Corporate Members by our Risk Management SIG with the aim of assessing the state of risk management in projects, with an emphasis on definitions and processes around opportunity management.
This report revealed the differences between the application of risk management for larger and smaller projects.
Related reading






APM Podcast
State of the art risk management projects: What you need to know
Emma meets Peter Simon, a Director at Lucidus Consulting and a member of the APM Risk SIG Committee.
He is co-author of a new APM report looking into opportunity management as part of the overall project risk management process. The findings reveal notable areas where what is defined in textbooks and standards do not match what’s happening in practice.
Publications
APM Body of Knowledge 7th edition
The APM Body of Knowledge 7th edition is a foundational resource providing the concepts, functions and activities that make up professional project management. It reflects the developing profession, recognising project-based working at all levels, and across all sectors for influencers, decision makers, project professionals and their teams.
You may also be interested in

The APM Learning portal is an online resource which provides members with access to digital guides, modules and other digital learning resources as part of the membership benefit.


Project – APM's official journal – is circulated quarterly for members only, and online for regularly updated news, blogs, opinions and insights for those in the project community.